Anonymizing social network data
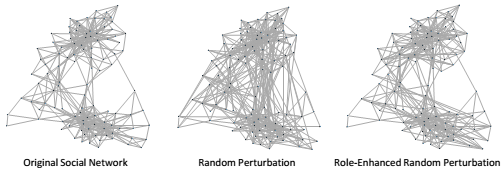
Study of social networks is growing in different domains such as academia, business, and even government, in order to identify interesting patterns at either the node or network levels. In many social network datasets, the exact identity of the involved people does not matter to the purpose of the study. Yet such datasets may carry sensitive information, and hence adequate measures should be in place to ensure protection against reidentification. Recent work in the literature has shown that structural patterns can assist in reidentification attacks on naively-anonymized social networks. Consequently, there have been proposals to anonymize networks in terms of structure to avoid such attacks. However, such methods usually introduce a large amount of distortion to the social network datasets, thus, raising serious questions about their utility for useful social network analysis. This research focuses on improving anonymization methods in terms of utility without sacrificing the privacy guarantees.
- A. Masoumzadeh and J. Joshi, “Top Location Anonymization for Geosocial Network Datasets,” Transactions on Data Privacy, vol. 6, no. 1, pp. 107–126, 2013.
- A. Masoumzadeh and J. Joshi, “Preserving Structural Properties in Edge-Perturbing Anonymization Techniques for Social Networks,” IEEE Transactions on Dependable and Secure Computing, vol. 9, no. 6, pp. 877–889, Nov. 2012.
- A. Masoumzadeh and J. Joshi, “Anonymizing Geo-Social Network Datasets,” in Proceedings of the 4th ACM SIGSPATIAL International Workshop on Security and Privacy in GIS and LBS - SPRINGL ’11, 2011, pp. 25–32 (Best Student Paper).
- A. Masoumzadeh and J. Joshi, “Preserving Structural Properties in Anonymization of Social Networks,” in Proc. 6th International Conference on Collaborative Computing: Networking, Applications and Worksharing (CollaborateCom), 2010, pp. 1–10.
